When rolling out an application, data security is always a concern. The Impersonate feature allows you to define a Security Admin who can sign in as another user to review their access rights permissions.
What does Impersonate do?
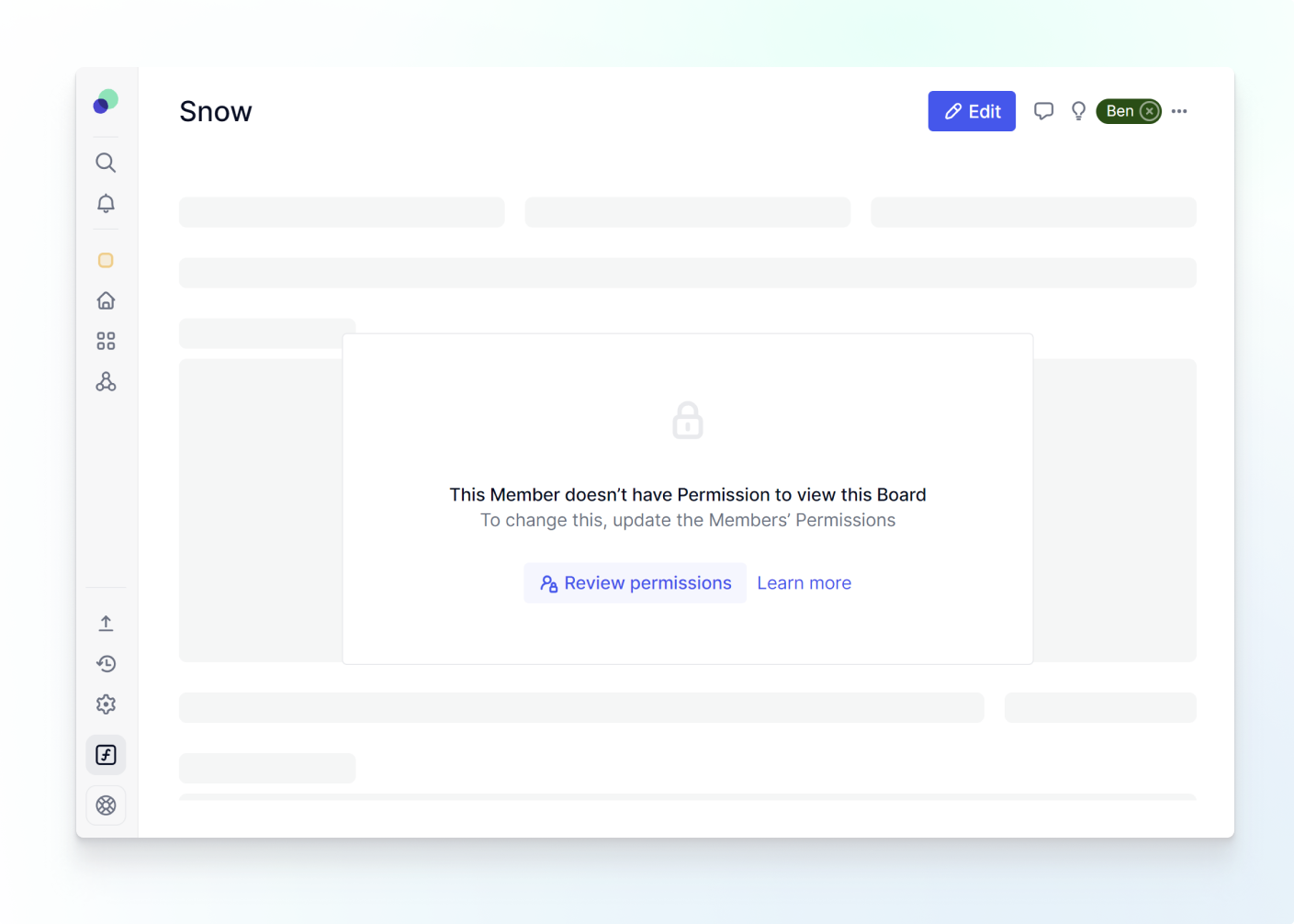
Impersonate allows users with the Security Admin account type to be able to “Login as” another individual. This will allow them to see what the other user can see. This is a powerful way to check the Access Rights they have applied to them. When signed in as another user, you will still have the permissions from your original account. Essentially, you will be able to check their access rights but not to be able to see which permissions they have assigned to them. You can also use Impersonate to view if a Member has access to a Board.
Who can Impersonate?
There are two account types that can Impersonate, the Primary Owner and Security Admin. The Primary Owner must first assign a user the Security Admin account type. After that, the Security Admin can assign others that account type. When a user is given the Account type of Security Admin, this setting applies to the entire Workspace. However, a Security Admin can not gain access to an Application they are not given permissions into. For example, if Pierre is a Security Admin, but does not have a role in a HR application, he would not be able to see this application nor use the impersonate feature in it.
How to Impersonate?
First, make sure you have the correct Security Admin Account type. Next, there are two ways to activate the Impersonate feature.
From Boards
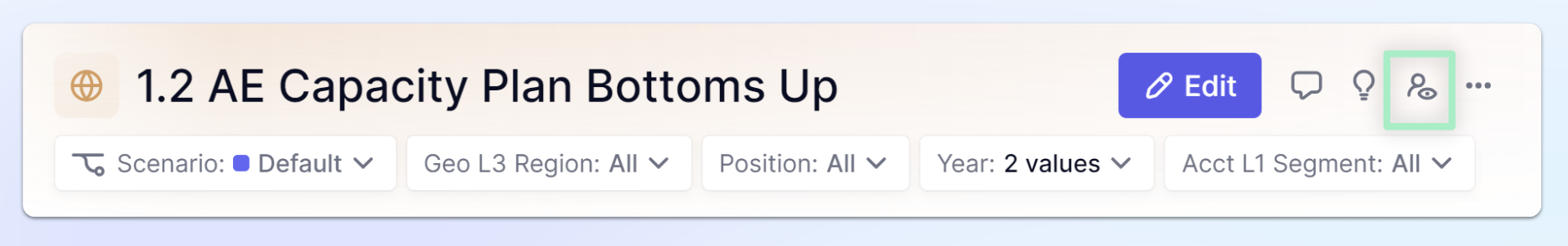
You can easily activate Impersonate from a Board. In the top right, select the Impersonate icon, then choose the user whose Access Rights you want to review.
When impersonating an individual who is adding an item on a list (directly on the list or through a form), it may appear that a user has write access when they do not. It may happen with certain AR configurations applied to “List Item Values” in Lists. If you encounter this, you will have to use a separate test user account.
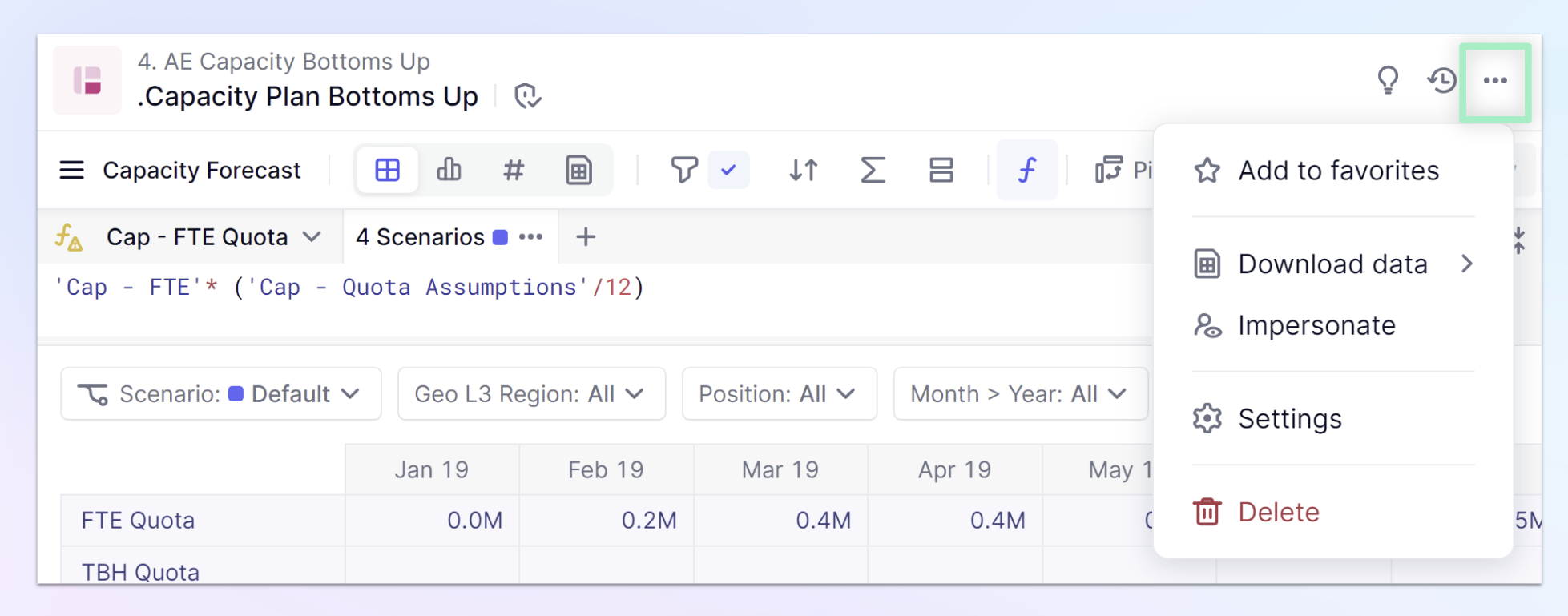
From Blocks
Once in a block, you’ll see an icon appear in the top right. Click the … menu to access the Impersonate.
Turning off Impersonate
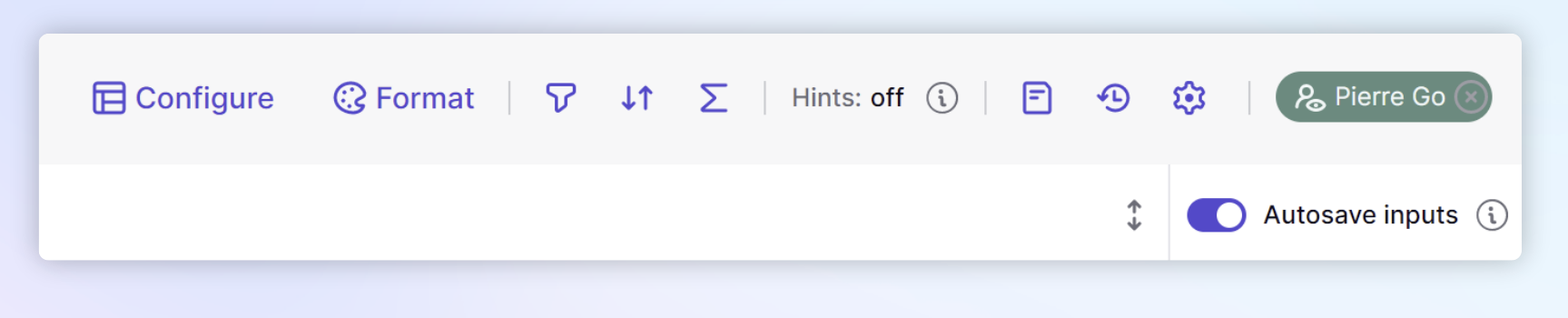
When you are done, you can click the X next to the name of the person you were impersonating to go back to your user settings.
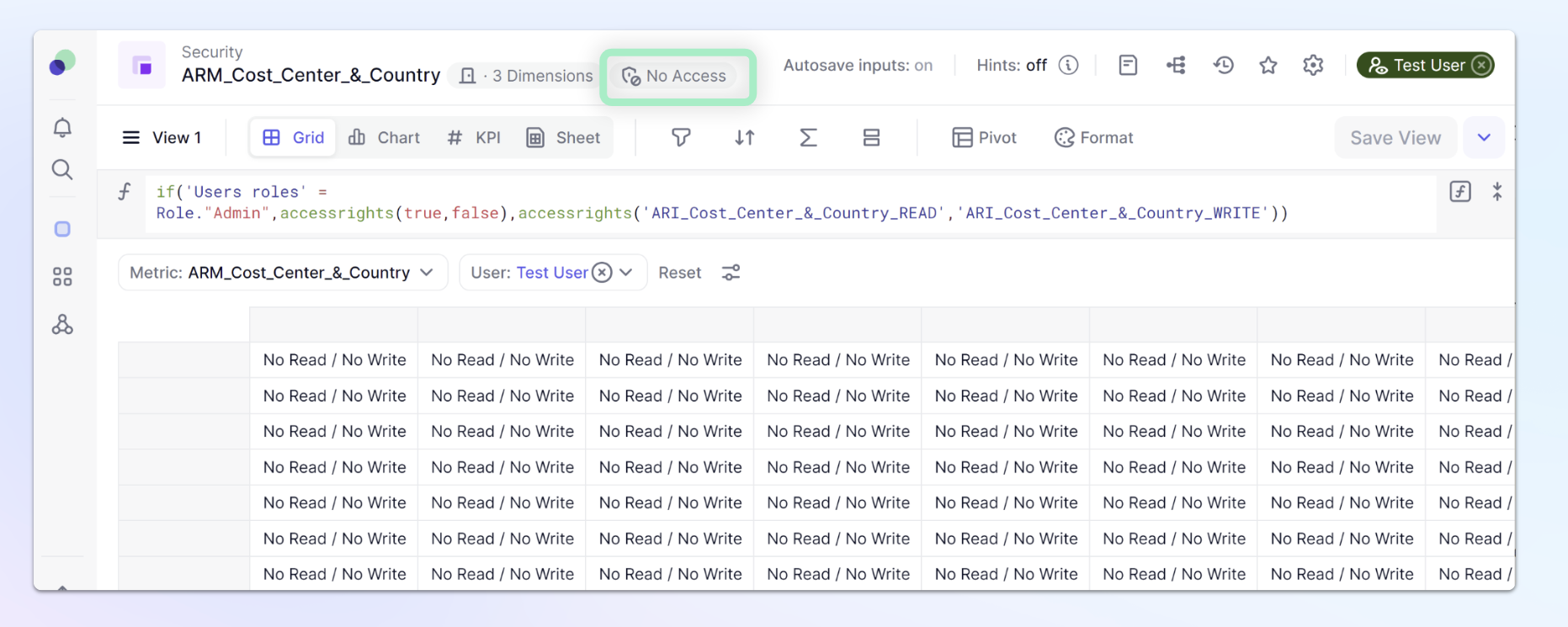
Impersonate on Access Rights Metrics
When impersonating a Member who does not have the proper access to view an Access Rights Metric, the Metric will always appear as saying “No Read/ No Write” even if the actual values are different. You can use the Access rights chip located at the top to identify if the impersonated user has access.
In this example, you can see the Member has No Access to this Access Rights Metric so the cells will all read as “No Read / No Write”. In other Metric types, the values would be blank.